Enable Remote Desktop remotely by using the registry
A few times I have encountered the fact that I cannot access a remote workstation or server by Remote Desktop (RDP). To solve this you can enable RDP trough a registery key remotely. The following steps can be taken to enable RDP remotely.
- Log in on a computer or server as an Domain Admin and open Regedit as an administrator.
- On the File menu, click Connect Network Registry.
- In the Select Computer dialog box, under Enter the object name to select, type the computer name and then click Check Names.
- After the computer name resolves, click OK.
- In the computer node that appears in the Registry Editor, navigate to HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server.
- In the console tree, click Terminal Server, and then, in the details pane, double-click fDenyTSConnections.
- In the Edit DWORD Value box, in Value data, type 0, and then click OK. This value enables connections at the level that allows connections from computers running any version of Remote Desktop.
To implement the change, restart the server or workstation remotely, as follows:
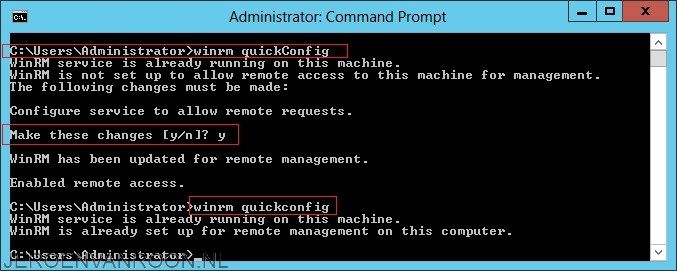
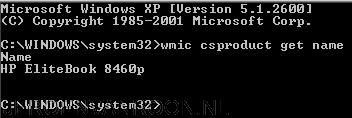
- Log in on a computer or server as an Domain Admin and open Command Prompt as an administrator.
- At the command prompt, type the following command: shutdown /m \\[Name of computer that has to be rebooted] /r