Recreate default mailboxes Exchange 2013
A few weeks ago I have installed an Exchange 2013 environment. After several weeks some strange behaviour started. Exchange was giving me errors when configuring several tasks. It seems like some of the internal databases or mailboxes were corrupted. To resolve this I have re-created the system mailboxes.
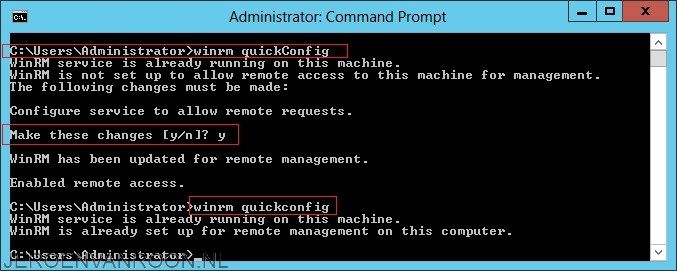
Step 1
Remove all Exchange mailboxes from the Active Directory Users and Computers console.
![2015-03-15 13_14_13-Remote Desktop Manager Free [TSC-RDS]](http://www.jeroenvanroon.nl/wp-content/uploads/2015/03/2015-03-15-13_14_13-Remote-Desktop-Manager-Free-TSC-RDS.png)
Step 2
Prepare Active Directory by running Microsoft Exchange 2013 Setup with the /PrepareAD switch in the root domain of your Active Directory forest. Make sure you are using the same version of the Exchange setup as the version that is installed. I have used the following command. Make sure you replace the “ExchangeName” with the name of your Exchange organisation.
- Setup.exe /PrepareAD /OrganizationName:”ExchangeName” /IAcceptExchangeServerLicenseTerms
After Setup finishes preparing Active Directory for Exchange, you’ll need to wait while Active Directory replicates the changes to all of your domain controllers.
Step 3
Re-enable the mailboxes with the Exhange Management Shell PowerShell module. Use the following commands:
- Enable-Mailbox –Arbitration “SystemMailbox{1f05a927-53ec-455e-b236-02df87905326}”
- Enable-Mailbox –Arbitration “SystemMailbox{bb558c35-97f1-4cb9-8ff7-d53741dc928c}”
- Enable-Mailbox –Arbitration “SystemMailbox{e0dc1c29-89c3-4034-b678-e6c29d823ed9}”
- Enable-Mailbox –Arbitration “FederatedEmail.4c1f4d8b-8179-4148-93bf-00a95fa1e042”
- Enable-Mailbox –Discovery “DiscoverySearchMailbox {D919BA05-46A6-415f-80AD-7E09334BB852}”
Make sure you replace the GUID’s with the GUID’s that are created in your environment. You can look these GUID’s up in the Active Directory Users and Computers console after running the /PrepareAD command.

![2015-03-15 12_22_45-Remote Desktop Manager Free [TSC-RDS]](http://www.jeroenvanroon.nl/wp-content/uploads/2015/03/2015-03-15-12_22_45-Remote-Desktop-Manager-Free-TSC-RDS.png)
![2015-03-15 12_57_12-Remote Desktop Manager Free [TSC-RDS]](http://www.jeroenvanroon.nl/wp-content/uploads/2015/03/2015-03-15-12_57_12-Remote-Desktop-Manager-Free-TSC-RDS.png)
![2015-03-15 12_57_21-Remote Desktop Manager Free [TSC-RDS]](http://www.jeroenvanroon.nl/wp-content/uploads/2015/03/2015-03-15-12_57_21-Remote-Desktop-Manager-Free-TSC-RDS.png)